Unfavorable-Semicircle-Wiki
POINT
♐POINT is a series of videos uploaded to the Twitter account. It began on January 29, 2017 and stopped posting on February 13th (at ♐POINT 5818). It was posted in parallel with the MOTH series being posted on the second youtube account. The series was the final series posted to Twitter before the manual closing of the account.
This video or series has a composite with an “interesting” video scope.
Description of videos
Similar to series such as NIL, the videos in this series are four seconds long, with the Unknown Voice saying a letter or a number at the beginning of the video.
Posting Frequency
The series was posted in ten bursts, with periods of inactivity in between. The busts were as short as 29 tweets and as long as 1488. In most periods, one video would be posted approximately every two minutes (with the exception of the third burst, which featured one video per minute).
Data pertaining to the periods can be found at Tomas’ website.
Composites
2-D Composites
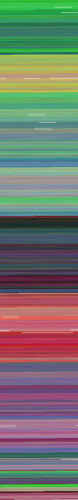
(♐POINT composite, complete to ♐POINT 5818)
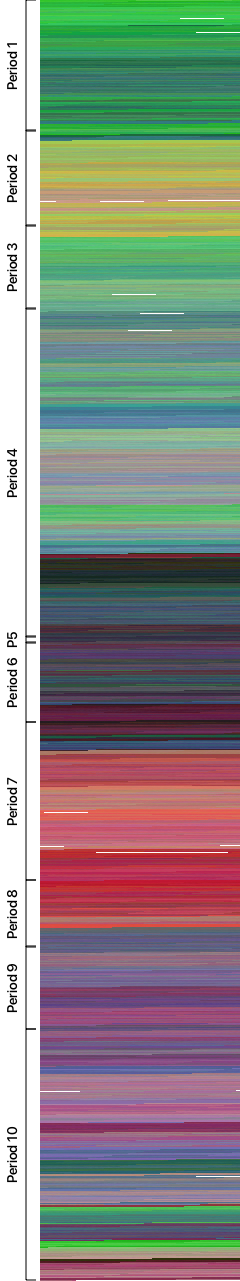
(♐POINT composite annotated with “periods” described above, complete to ♐POINT 5818)
3-D Composites
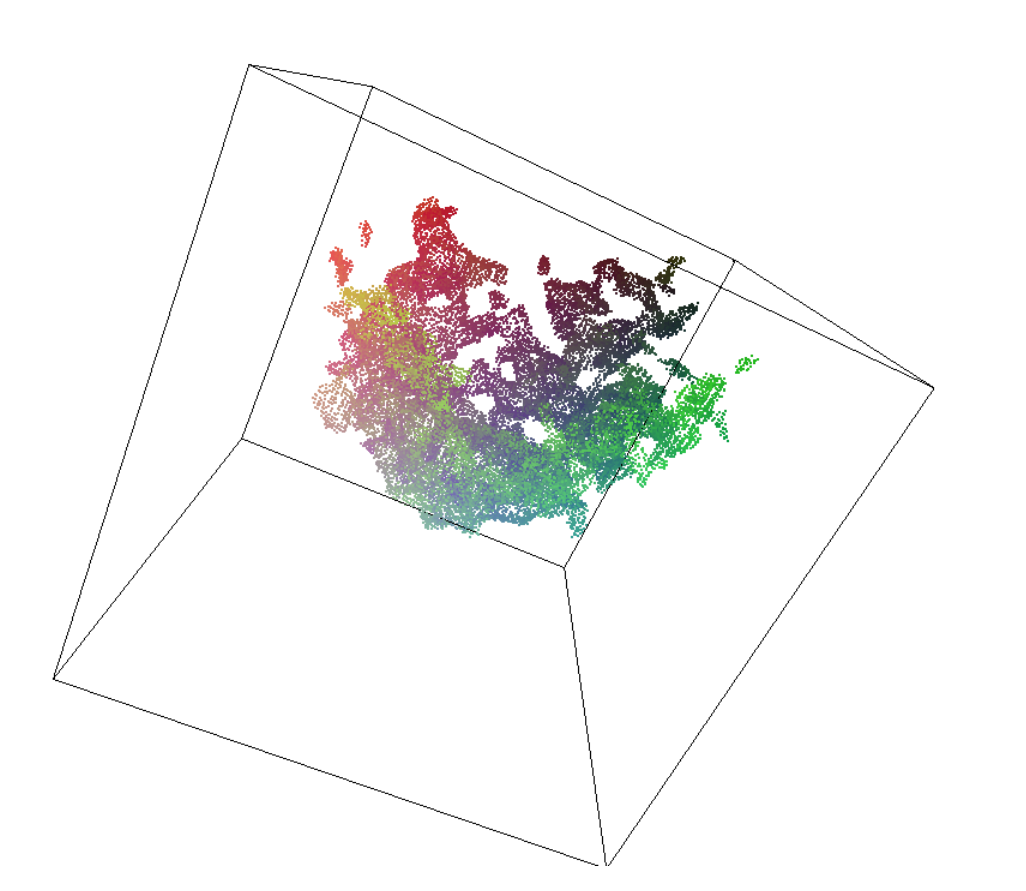
screencap of ♐POINT 3-D composite (view 1)
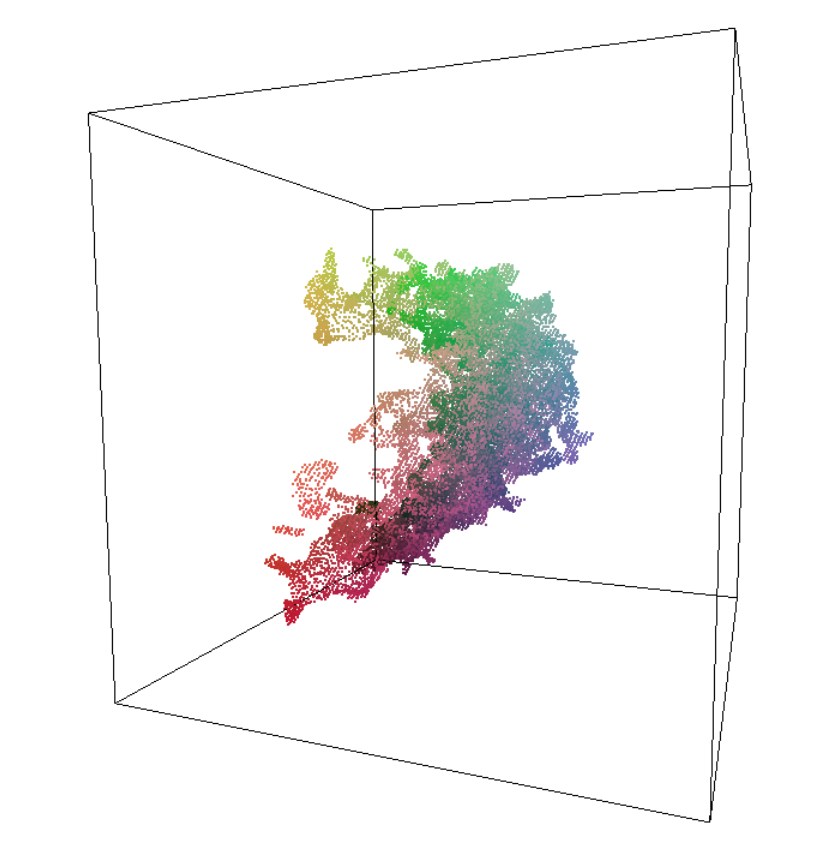
screencap of ♐POINT 3-D composite (view 2)
The 3-D composite makes a roughly half-spherical shape, somewhat similar to that of ♐DUAL’s 3-D composite. This (and other) 3-D composites are viewable here.
Transcription
Using audio hashing, Thomas has auto-transcribed the entire series. It is backed up on the wiki here.
Character frequency
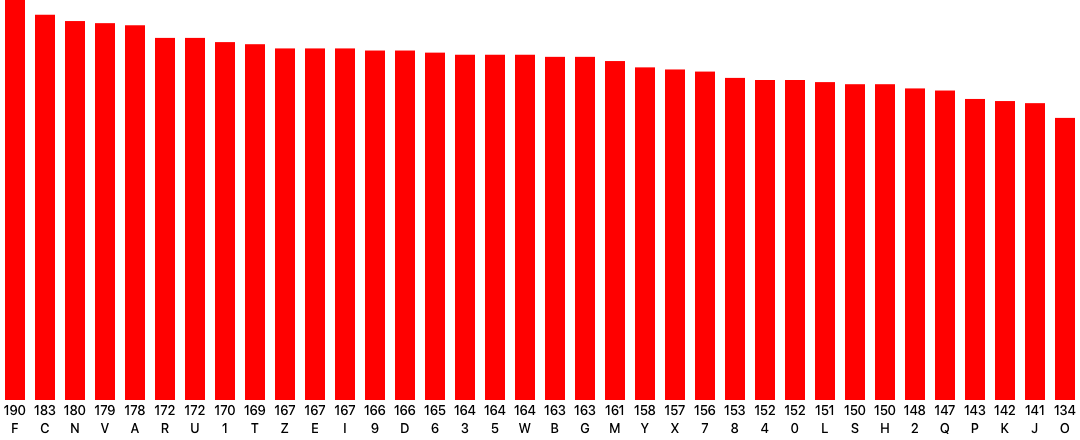
(Tomas’ analysis shows the frequency of each character in the ♐POINT transcription, complete to ♐POINT 5818)
Possible cipher data
Caesar cipher
Using a Caesar Cipher tool, ShadowMorphyn has found the possible references to two other UFSC videos (LOVE and JALVINSACH) with a 22 character shift.
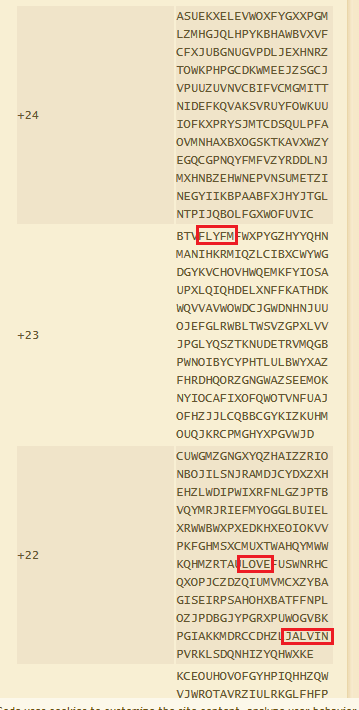
(Screencap of brute-forcing the ♐POINT transcription as a Caesar Cipher)
Bifid cipher
The transcription also corresponds closely with a Bifid cipher using a 6×6 Polybius square, according to a cipher comparison utility.
For more investigation, a brute force or dictionary attack can be done using the CryptoCrack utility.
Links
A partial archive (3250 videos) of the series is available here.